Are Screenshots Admissible in Court? Complete Guide for Lawyers
Yes, but only with proper authentication. Learn how to collect, preserve, and present screenshot evidence that meets Federal Rules of Evidence standards.
Digital evidence requires proper handling to be court-admissible. Key requirements: (1) Capture immediately using forensic tools that preserve metadata, (2) Maintain chain of custody documentation for every access, (3) Use cryptographic hashes (SHA-256) to prove integrity, (4) Obtain blockchain timestamps for temporal proof. Bottom line: Simple screenshots without cryptographic verification will be challenged. Federal Rules of Evidence Rule 901(b)(9) requires proof that your capture process produces accurate results.
What You'll Learn in This Guide
How do I collect digital evidence for court? To ensure your digital evidence is admissible, follow these 5 critical steps:
- → Capture immediately: Use forensic tools the moment you discover evidence – web content changes constantly
- → Preserve metadata: URLs, timestamps, HTTP headers, TLS certificates are as important as visual content
- → Use cryptographic hashes: SHA-256 creates unique fingerprints proving integrity
- → Obtain blockchain timestamps: Immutable proof of when evidence existed
- → Document chain of custody: Record every access, transfer, and storage location
Under Federal Rules of Evidence Rule 901(b)(9), electronic records must be authenticated through "evidence describing a process that produces an accurate result."
Warning: Regular Screenshots Are Increasingly Challenged
Courts and opposing counsel regularly challenge simple screenshots as evidence. Common objections: "Screenshots can be edited", "No proof of when it was taken", "Metadata can be manipulated". The landmark case Lorraine v. Markel (2007) established that electronic evidence requires authentication showing the capture process is reliable. Without cryptographic proof, your evidence may be inadmissible or significantly weakened.
People Also Ask
How do I collect digital evidence for court? ▼
To collect court-admissible digital evidence: 1) Capture immediately using forensic tools that preserve metadata, 2) Document circumstances in writing, 3) Maintain chain of custody for every access and transfer, 4) Use cryptographic hashes (SHA-256) to prove integrity, 5) Obtain blockchain timestamps for temporal proof, 6) Store securely with backups in multiple locations, 7) Verify integrity before court presentation.
What is chain of custody for digital evidence? ▼
Chain of custody is the documented chronological history of evidence handling from capture to court presentation. It records who collected the evidence, who has accessed it, when transfers occurred, and how it was stored. A broken chain of custody can render evidence inadmissible because it creates doubt about authenticity and integrity.
What are the Federal Rules of Evidence requirements for digital evidence? ▼
Under the Federal Rules of Evidence, digital evidence must meet several criteria: Relevance (Rule 401), Authentication (Rule 901) proving the evidence is genuine, Hearsay exceptions (Rules 801-807) for business records, and the Best Evidence Rule (Rule 1002) requiring original or reliable duplicate. Rule 901(b)(9) specifically allows authentication through "evidence describing a process or system and showing that it produces an accurate result."
Why is cryptographic verification important for digital evidence? ▼
Cryptographic verification is essential because digital data can be easily modified without visible traces. SHA-256 hashes create unique fingerprints proving data integrity – any change produces a completely different hash. Digital signatures prove who created the evidence (authenticity), and blockchain timestamps prove when it existed. These three elements together meet authentication requirements under Federal Rules of Evidence.
What are common mistakes when collecting digital evidence? ▼
Common pitfalls include: 1) Modifying screenshots (even cropping raises authenticity questions), 2) Missing metadata (timestamps and URLs are critical), 3) Broken chain of custody (gaps in documentation weaken cases), 4) Using consumer screenshot tools (lacking cryptographic verification), 5) Delayed capture (web content changes constantly – "I saw it yesterday" won't hold up in court).
What is the Lorraine v. Markel case and why does it matter? ▼
Lorraine v. Markel American Insurance Co. (2007) is a landmark U.S. federal court decision that established comprehensive standards for authenticating electronic evidence. The court identified five hurdles: relevance, authenticity, hearsay, original/best evidence, and unfair prejudice. It established that electronic evidence requires proof of a reliable capture process – simple screenshots without cryptographic verification are increasingly insufficient.
How do I preserve social media evidence for a lawsuit? ▼
To preserve social media evidence for a lawsuit: 1) Capture immediately using forensic tools that preserve metadata (timestamps, URLs, user info), 2) Include profile pages, not just individual posts, 3) Document privacy settings that allowed access, 4) Send a preservation letter to opposing counsel, 5) Never delete or modify any content after litigation is foreseeable. Courts can impose severe sanctions for spoliation of evidence – in Lester v. Allied Concrete, fines exceeded $700,000 for deleting Facebook photos.
Can text message screenshots be used as evidence in court? ▼
Yes, text message screenshots can be used as evidence if properly authenticated. Following United States v. Avenatti (2021), courts accept screenshots of text messages when authenticated the same way as actual messages. You need: 1) Witness testimony that screenshots are true to what was received, 2) Identification of the sender (phone number, contact name, distinctive characteristics), 3) Date and time clearly visible, 4) Metadata preservation when possible. Courts may require phone records or forensic extraction for high-stakes cases.
How do I prove when a screenshot was taken? ▼
To prove when a screenshot was taken: 1) Use blockchain timestamping services like OpenTimestamps that create immutable proof anchored to Bitcoin, 2) Preserve file metadata (creation date, modification date), 3) Include visible timestamps in the capture (browser time, page timestamps), 4) Use forensic capture tools that automatically record capture time with cryptographic verification, 5) Have a neutral witness observe and document the capture. Simple screenshots without cryptographic timestamps can have their timing easily challenged.
How do I document evidence for a defamation case? ▼
For defamation cases, document evidence immediately as online content can be deleted within minutes: 1) Screenshot the full page including author name, timestamp, and URL, 2) Record video of scrolling through the defamatory content, 3) Save the webpage using browser's "Save As" function, 4) Generate cryptographic hashes (SHA-256) immediately upon collection, 5) Archive using services like Archive.today or Perma.cc, 6) Document witness statements from those who saw the posts, 7) Preserve notifications and any responses showing the content spread.
What is the United States v. Vayner case about screenshot evidence? ▼
In United States v. Vayner (2014), the U.S. Court of Appeals for the Second Circuit overturned a conviction because a social media screenshot was not properly authenticated. The prosecution submitted a printout of a VK.com page, but couldn't prove the page actually belonged to the defendant or that it hadn't been fabricated. This case established that screenshots require proper authentication – you must prove the evidence is what it purports to be, not just that it looks authentic.
Will the attacker see that I captured evidence with ProofSnap? ▼
No. ProofSnap captures evidence completely discreetly. The extension works locally in your browser – it does not interact with the platform's servers or send any notifications. The person who sent the harassing messages, threats, or defamatory content has no way of knowing you captured evidence. There are no read receipts, no "screenshot taken" alerts, and no activity logs visible to the other party. This is crucial for victims of cyberbullying, harassment, or domestic abuse who fear retaliation if the abuser discovers evidence is being collected.
What if the harasser blocked me before I could capture evidence? ▼
Once blocked, you typically lose access to direct messages and the person's profile on most platforms. This is why immediate evidence capture is critical – document harassment as soon as it occurs. However, you may still have options: 1) Check your email notifications – many platforms send copies of messages, 2) Request your data archive from the platform (GDPR/CCPA rights), 3) Some platforms preserve message history even after blocking (e.g., WhatsApp), 4) If you took regular screenshots before, they can still be authenticated. The key lesson: never delay evidence capture. If you're being harassed, document everything immediately, even if you think it might escalate – waiting until "it gets worse" often means losing crucial early evidence.
Can I capture evidence on my mobile phone? ▼
ProofSnap is a Chrome browser extension, so it works on desktop/laptop computers. However, most harassment happens on mobile – here's how to capture mobile evidence: 1) WhatsApp: Open WhatsApp Web (web.whatsapp.com) on your computer and capture from there, 2) Instagram/Facebook: Log in through Chrome on desktop to access your DMs, 3) Telegram: Use Telegram Web or the desktop app, 4) iMessage: If you have a Mac, messages sync automatically, 5) SMS: Forward messages to email, or use Android Messages for Web. For platforms without web access, take mobile screenshots first as backup, then use ProofSnap on any web-accessible version for forensic-grade evidence with full authentication.
I. The Importance of Proper Evidence Collection
Digital evidence is increasingly critical in modern legal proceedings. However, improper collection and preservation can render evidence inadmissible or unreliable. This guide outlines best practices to ensure your digital evidence stands up in court.
Case Study: Evidence Dismissed Due to Authenticity Questions
An attorney presented screenshot evidence of defamatory social media posts. The opposing counsel immediately challenged: "These images have no metadata, no timestamps, and could have been created this morning in Photoshop."
"Counsel, do you have any independent verification that these screenshots existed before litigation commenced?"
— Federal Court Judge, 2024
Result: Evidence weight significantly reduced. With blockchain-timestamped forensic captures, the attorney could have proven the evidence existed months before the lawsuit was filed.
See exactly what a court receives
Download a real evidence package — the same ZIP that gets submitted as proof. Or send any URL to support@getproofsnap.com and we'll capture it for you free.
Download Sample PackageII. Key Principles of Digital Evidence
What is Chain of Custody?
Chain of custody is the documented chronological history of evidence handling from the moment of capture to court presentation. It records who collected the evidence, who has accessed it, when transfers occurred, and how it was stored. A broken chain of custody can render evidence inadmissible because it creates doubt about authenticity and integrity.
Understanding these fundamental principles is essential for anyone collecting digital evidence:
- 1. Chain of Custody: Document every step of evidence collection and handling. Every person who touches the evidence must be documented.
- 2. Authenticity: Prove the evidence hasn't been altered or manipulated since collection. Use cryptographic tools when possible.
- 3. Reliability: Use tools and methods that are scientifically sound and widely accepted in the legal community.
- 4. Completeness: Capture all relevant metadata and context. Missing information can undermine the entire evidence package.
III. What ProofSnap Captures
ProofSnap goes beyond simple screenshots to provide comprehensive evidence packages that meet legal standards:
Complete Evidence Package Contents
IV. Admissibility Standards in Court
What are the Federal Rules of Evidence?
The Federal Rules of Evidence (FRE) are the rules governing the admissibility of evidence in U.S. federal courts. For digital evidence, Rule 901(b)(9) is particularly important – it allows authentication through "evidence describing a process or system and showing that it produces an accurate result." The landmark case Lorraine v. Markel (2007) established comprehensive standards for authenticating electronic evidence.
While admissibility varies by jurisdiction, digital evidence typically must meet these criteria:
Federal Rules of Evidence (U.S.)
- 401 Relevance: Evidence must be relevant to the case
- 901 Authentication: Evidence must be authenticated as genuine
- 801-807 Hearsay: Digital records may qualify as business records exception
- 1002 Best Evidence: Original or reliable duplicate required
How ProofSnap Helps Meet These Standards
- • Non-repudiable timestamps via Bitcoin blockchain
- • Independently verifiable evidence through OpenTimestamps
- • Complete audit trail of capture process
- • Standard cryptographic methods (RSA-4096, SHA-256)
- • Comprehensive documentation in PDF format
V. Recommended Workflow for Legal Professionals
Follow this step-by-step process to maximize admissibility:
1 Immediate Capture
Time is critical. Capture evidence immediately when discovered:
- • Install ProofSnap extension in advance
- • Click the capture button as soon as relevant content is found
- • Don't refresh or navigate away before capturing – content may change
- • Capture multiple times if the content is critical
2 Secure Storage
Protect the integrity of captured evidence:
- • Save the complete evidence package (ZIP file) to secure storage
- • Create backup copies on different media (cloud + local storage)
- • Never open or modify files within the evidence package
- • Use encryption for sensitive cases
3 Document the Circumstances
Create a contemporaneous record of the capture process:
- • Date and time of discovery
- • How you accessed the content (URL, search terms, links)
- • Why the content is relevant to your case
- • Any witnesses present during capture
- • Environmental conditions (location, device used)
4 Maintain Chain of Custody
Document every transfer and access:
- • Who captured the evidence
- • Who has accessed the files
- • When and why files were transferred
- • Storage locations and security measures
5 Verify Before Court
Before presenting evidence, verify its integrity:
- • Check the digital signature using the included public key
- • Verify the blockchain timestamp at opentimestamps.org
- • Confirm all file hashes match the manifest
- • Test the verification process with a colleague
VI. Common Pitfalls to Avoid
Modified Screenshots
Never edit screenshots or HTML files. Even cropping can raise authenticity questions. Capture the full page.
Missing Metadata
Timestamps and URLs are critical. Simple screenshots without metadata have limited value.
Broken Chain of Custody
Every gap in documentation weakens your case. Document everything.
Using Consumer Tools
Regular screenshot tools lack cryptographic verification. Use purpose-built evidence capture tools like ProofSnap.
Delayed Capture
Web content changes constantly. Capture immediately when found. "I saw it yesterday" won't hold up in court.
VII. Special Considerations
Social Media Evidence
- • Capture profile pages, not just individual posts
- • Include timestamps and engagement metrics
- • Document privacy settings that allowed access
- • Consider terms of service implications
Dynamic Content
- • Capture interactive elements multiple times showing different states
- • Document how you triggered content changes
- • Consider screen recording for highly dynamic content
International Considerations
- • EU GDPR: Be aware of data protection requirements
- • Cross-border discovery: Follow Hague Convention procedures
- • Local authentication standards: Verify requirements in your jurisdiction
- • Translation: Consider certified translation needs
VIII. The 30-Second Courtroom Verification
When you're in front of a judge, technical jargon like "SHA-256 hash" or "RSA-4096 signature" won't help you. What matters is: can you prove right now, in this courtroom, that the evidence is authentic?
Live Verification in 3 Steps
Open opentimestamps.org on any device
The court's computer, your phone, opposing counsel's laptop – it doesn't matter.
Upload the manifest.json.ots file from your evidence package
This is the blockchain timestamp proof file included in every ProofSnap capture.
Green checkmark confirms authenticity
The website shows the exact Bitcoin block and date when your evidence was timestamped – visible to everyone in the courtroom.
Why this matters: No expert witness needed. No technical explanation required. The judge sees an independent, public website confirm that your evidence existed at a specific date and time, anchored to the Bitcoin blockchain – the most secure and immutable ledger in the world.
IX. Self-Authentication: Skip the Expert Witness
In 2017, the Federal Rules of Evidence were amended to add Rules 902(13) and (14), which allow digital evidence to "authenticate itself" without requiring expert testimony.
What This Means for Your Case
FRE 902(13) – Certified Records
Records generated by an electronic process or system can be self-authenticating if accompanied by a certification showing the process produces an accurate result.
FRE 902(14) – Certified Data Copied
Data copied from an electronic device can be self-authenticating if certified by a qualified person that the copy is a complete and accurate copy.
How ProofSnap Meets These Requirements
- • Evidence PDF Report serves as certification document with all technical details
- • SHA-256 hash values prove the copy is identical to the original capture
- • Digital signature certifies the capture process and source
- • Blockchain timestamp provides independent third-party verification
Cost savings: Expert witness fees typically range from $300-$500 per hour, with trial testimony costing $2,000-$5,000 or more. Self-authenticating evidence under FRE 902(13)/(14) can eliminate this expense entirely.
X. The Web is Liquid: Why Speed Matters
The article tells you to "capture immediately" – but that doesn't fully convey the tragedy of lost evidence. Web content is ephemeral. It disappears.
Evidence Disappears in Seconds
Real Scenario: The Disappearing Defamation
A client discovers defamatory posts about their business at 9:00 AM. They call their lawyer at 9:15 AM. By 9:30 AM, when the lawyer checks the URL – the posts are gone. Deleted. No evidence.
With ProofSnap: One click at 9:00 AM captures everything – screenshot, HTML, metadata, and blockchain timestamp. Even if the content is deleted seconds later, you have court-admissible proof it existed.
ProofSnap advantage: Capture in one click. No need to manually save pages, copy URLs, take screenshots, and document timestamps separately. By the time you finish that workflow, the evidence might already be gone.
XI. ProofSnap vs. Wayback Machine (Archive.org)
Many people think Archive.org (the Wayback Machine) is sufficient for preserving web evidence. While it's a valuable resource, it has critical limitations for legal use.
| Feature | ProofSnap | Archive.org |
|---|---|---|
| Content behind login (Facebook, banking portals) | Yes | No |
| Private messages (WhatsApp Web, Messenger) | Yes | No |
| User-specific metadata (IP, browser, timezone) | Yes | No |
| Cryptographic hash (SHA-256) | Yes | No |
| Digital signature | Yes | No |
| Blockchain timestamp | Yes | No |
| Capture on demand (immediate) | Yes | Request-based |
| JavaScript-rendered content | Yes | Limited |
| Court-ready PDF evidence report | Yes | No |
Key Takeaway
Archive.org captures public web pages. ProofSnap captures what YOU see – including content behind logins, personalized pages, and private messages. For divorce cases (Facebook messages), employment disputes (HR portals), or financial fraud (banking dashboards), only ProofSnap can capture the evidence you need.
XII. What You Get: Sample Evidence Report
Every ProofSnap capture generates a comprehensive evidence package. Here's what the PDF Evidence Report looks like – the document you can present in court.
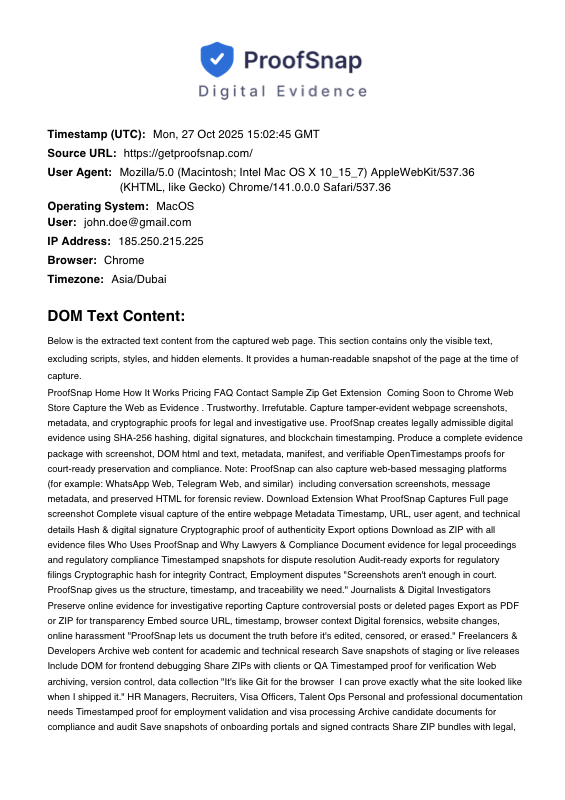
Click to enlarge. Download full sample PDF
What the Evidence Report Contains
Header Section
- • ProofSnap logo and branding
- • "Digital Evidence" designation
- • Professional formatting for court presentation
Capture Metadata
- • Exact UTC timestamp
- • Full source URL
- • User agent, browser, OS
- • IP address and timezone
Content Sections
- • Extracted DOM text (searchable)
- • Full-page screenshot
- • Complete HTML source (in ZIP)
Legal Notice
- • Integrity and authenticity statement
- • Reference to digital signatures
- • Blockchain timestamp verification note
Complete Evidence Package (ZIP) also includes: manifest.json (file hashes), manifest.sig (digital signature), manifest.json.ots (blockchain timestamp proof), publickey.pem, screenshot.jpeg, page.html, domtextcontent.txt, and metadata.json.
Key Takeaways: Digital Evidence Best Practices
- 1. Capture immediately – Web content changes constantly. Use forensic tools the moment you discover relevant evidence.
- 2. Maintain chain of custody – Document every access, transfer, and storage location. Gaps can render evidence inadmissible.
- 3. Use cryptographic verification – SHA-256 hashes prove integrity, digital signatures prove authenticity, blockchain timestamps prove when.
- 4. Preserve all metadata – URLs, timestamps, HTTP headers, TLS certificates are often as important as the visual content.
- 5. Federal Rules of Evidence Rule 901 – Electronic records must be authenticated through evidence showing the process produces accurate results.
Evidence Collection Checklist
When collecting digital evidence with ProofSnap, ensure you:
- • Capture immediately upon discovery
- • Save the complete evidence package securely
- • Document circumstances in writing
- • Maintain clear chain of custody
- • Verify integrity before court presentation
- • Never modify the original files
- • Keep backups in multiple locations
- • Consult with legal counsel about admissibility
Legal Disclaimer: This guide provides general information about digital evidence best practices. It does not constitute legal advice. Admissibility of evidence depends on your jurisdiction, the specific judge, proper chain of custody, and other factors. Always consult with a qualified attorney regarding your specific case.
Start Collecting Legal-Grade Evidence
Install ProofSnap and capture evidence that meets legal standards with blockchain verification.