How to Document Online Scams for Police, Banks & Courts — The 2026 Evidence Guide
Scam websites disappear in hours. Fake profiles get deleted. Banks reject screenshots. Here is the step-by-step guide to capturing forensic evidence of online fraud that police, banks, and courts actually accept — before it vanishes forever.
Within 5 minutes:
- 1. CALL YOUR BANK — request a block or chargeback. The faster you act, the higher the chance of stopping the transaction.
- 2. DON'T CLOSE ANYTHING — don't close tabs, don't delete messages, don't confront the scammer.
- 3. CAPTURE EVIDENCE — the scam page, all communications and payment proof (step-by-step guide).
Key contacts:
- • Bank of America: 1-800-732-9194
- • Chase: 1-800-935-9935
- • Wells Fargo: 1-800-869-3557
- • Citi: 1-800-950-5114
- • Capital One: 1-800-227-4825
- • FTC Report Fraud: reportfraud.ftc.gov
- • FBI IC3: ic3.gov
- • Emergency: 911
For wire transfers, action within 24 hours drastically increases your chances of recovery through the bank's recall system. For card payments, you have 120 days for a chargeback — but the sooner you report, the better.
Online fraud is the largest crime category in the developed world. In 2024, the FBI’s IC3 received 859,532 complaints reporting $16.6 billion in losses — a 33% increase from 2023. The FTC reported $12.5 billion in consumer fraud losses. In the UK, 3.9 million fraud incidents were recorded, accounting for 41% of all crime. In the EU, payment fraud reached €4.2 billion.
Sources: FBI IC3 2024 Annual Report, FTC Consumer Sentinel 2024, UK Finance 2024, EBA/ECB 2025 Report, Pew Research 2025
Quick Answer: What Evidence Do You Need?
Bottom line: If you have been scammed online, do not close your browser tabs. Capture the scam website, all conversations, and payment records with a forensic tool that generates SHA-256 hashes and blockchain timestamps. Then contact your bank and file a report with IC3 (US) or Report Fraud (UK).
Police, banks, and courts need four things from scam victims: (1) timestamped captures of the scam website/profile/listing before it disappears, (2) complete communication records with the scammer, (3) payment documentation (bank statements, crypto wallet addresses, receipts), and (4) chain of custody proving the evidence has not been altered.
A regular screenshot provides only #1 partially (no metadata, no timestamp proof, no tamper detection). Forensic capture provides all four. See the quick reference checklist for a printable step-by-step action plan.
Already Been Scammed? Here Is What You Can Still Capture
If the scam website is already gone and the profile is deleted, you are not out of options. There is still evidence you can secure right now:
Still available (capture NOW)
- • Your bank/card statement showing the transaction
- • Email confirmations (order, payment, shipping)
- • Chat histories that still exist (WhatsApp, email, Messenger)
- • PayPal/Venmo/Zelle transaction receipts
- • Crypto wallet transactions on blockchain explorers
- • The scam site on the Wayback Machine or Google Cache
Still in your browser
- • Browser history (proves you visited the scam URL)
- • Downloaded files (invoices, contracts, images)
- • Autofill data (the credentials you entered)
- • Notification/SMS screenshots on your phone
- • Search engine results still showing the scam listing
- • Social media posts/ads that led you to the scam
Capture each of these pages with a forensic tool right now — every piece adds weight to your police report, bank dispute, and chargeback claim. A timestamped capture of your bank statement page is already stronger evidence than a plain screenshot.
Capture what’s left with ProofSnap →Table of Contents
- Why Do Screenshots Fail as Scam Evidence?
- Seven Types of Online Scams & How to Document Each
- How Do You Capture Evidence of an Online Scam?
- Where Do You Report an Online Scam? (IC3, Action Fraud & Global Agencies)
- How to Get a Chargeback After Fraud (Visa 13.3, Mastercard 4853)
- Legal Standards: FRE 901, eIDAS 2 & Court Admissibility
- Prevention: What to Do Before You Pay
- After a Scam: Protect Yourself from Further Damage
- Screenshot vs. Forensic Evidence: What Gets Accepted?
- FAQ (14 Questions)
- Sources & References
1. Why Do Screenshots Fail as Scam Evidence?
When you realize you have been scammed, your first instinct is to take a screenshot. It feels like proof. But in 2026, a plain screenshot is the weakest form of digital evidence you can present to police, your bank, or a court. Here is why:
No Timestamp Proof
A screenshot’s file creation date can be changed. There is no independent proof of when the capture was taken. The scammer can claim the page looked different at the time of the transaction.
Easily Fabricated
Browser DevTools let anyone edit the visible content of any web page in seconds. Photoshop and AI tools can generate pixel-perfect fake screenshots. Courts know this.
No Metadata
Screenshots lack HTTP headers, TLS certificate data, cookies, server response codes, and page HTML. This metadata is what connects the visual content to a specific server at a specific time.
No Chain of Custody
There is no record of how the screenshot was created, stored, or handled. Under FRE 901, the opposing party can challenge its authenticity.
The core problem: Scam websites disappear in hours. Phishing pages average just 21 hours online. Fake online shops typically operate for 2–8 weeks before moving to a new domain. Romance scam profiles are deleted within hours of being reported. Once the content is gone, a screenshot is all you have — and it may not be enough.
Still have the scam page open? Capture it now — before it disappears.
Your bank needs timestamped proof of what the seller promised. ProofSnap creates a court-ready evidence package in one click — screenshot, metadata, SHA-256 hash, blockchain timestamp, and PDF. Free for 7 days.
See exactly what a court receives
Download a real evidence package — the same ZIP that gets submitted as proof. Or send any URL to support@getproofsnap.com and we'll capture it for you free.
Download Sample Package2. Seven Types of Online Scams & How to Document Each
Each scam type requires different evidence. Here is what to capture for the seven most common categories, ranked by 2024 losses:
Investment & Crypto Scams (“Pig Butchering”)
$9.3B losses (FBI, 2024)Victims are recruited through dating apps or social media, build a relationship with the scammer, and are directed to a fake investment platform. The FBI’s Operation Level Up identified over 4,300 victims, with 77% unaware they were being scammed.
What to capture:
- • The fake investment platform (login page, dashboard, account balance, transaction history)
- • The scammer’s crypto wallet addresses (search on Etherscan or Blockchain.com)
- • All communication: dating app messages, WhatsApp/Telegram chats, Signal conversations
- • The original recruitment message or ad
- • Any “withdrawal blocked” or “tax payment required” messages
- • Bank transfer or crypto transaction confirmations
Imposter Scams (Government, Bank, Tech Support)
$2.95B losses (FTC, 2024)Scammers impersonate the IRS, HMRC, your bank, Amazon, or Microsoft. They create urgency (“your account will be closed”) to make you act before thinking. The FTC reports a four-fold increase in impersonation scam losses among older adults from 2020 to 2024.
What to capture:
- • The phishing email with full headers (in Gmail: “Show original”; in Outlook: “View message source”)
- • The fake website they linked to (note the URL — often one letter off from the real site)
- • Any phone numbers or callback numbers provided
- • Text messages or voicemails from the scammer
- • Remote access software installed (TeamViewer, AnyDesk session logs)
- • Payment receipts (gift cards, wire transfers, crypto)
Fake Online Shops & E-Commerce Scams
$432M losses (FTC, 2024)Fake websites mimic legitimate brands, accept payment, and either ship counterfeit goods or nothing at all. Global e-commerce fraud losses are projected to reach $48 billion in 2025. These sites typically operate for 2–8 weeks before disappearing.
What to capture:
- • The product listing page (price, description, images, seller info)
- • The checkout and order confirmation page
- • The website’s contact page, terms of service, and “About Us” page
- • Your order confirmation email
- • Any tracking numbers provided (often fake)
- • WHOIS data for the domain (check domain age — scam sites are typically days or weeks old)
Romance Scams
$672M losses (FBI, 2024)The FBI reports that scammers increasingly use AI to generate realistic photos, videos, and voice messages. The FBI San Francisco reported losses in their territory doubled from $22M (2024) to $40M+ (2025).
What to capture:
- • The scammer’s dating/social media profile (photos, bio, claimed location, joined date)
- • All messaging conversations with timestamps
- • Reverse-image search results (Google Images, TinEye) showing stolen photos
- • Any websites or investment platforms they directed you to
- • Payment receipts, gift card numbers, wire transfer confirmations
- • Video call screenshots if deepfake was used (note visual artifacts)
Critical: Capture everything before confronting the scammer or reporting the profile. They will delete everything immediately.
Facebook Marketplace, eBay & Classified Scams
34% of FB Marketplace ads may be scamsAmericans have lost $2.7 billion to social media scams since 2021 (FTC). Fraud researchers found that approximately 34% of Facebook Marketplace ads could be scam posts, with an average of 6 fake ads posted per minute.
What to capture:
- • The listing page (item title, price, photos, seller profile link)
- • The seller’s profile (account age, other listings, reviews/ratings)
- • All Messenger/platform chat messages
- • Payment method used (Zelle, Venmo, PayPal “Friends & Family”, Cash App)
- • Any shipping or tracking information
- • The item received (if different from listing — photograph for comparison)
Phishing & Smishing (Text Scams)
$470M text scam losses (FTC, 2024)Fake package delivery notifications, unpaid toll warnings, bank “fraud alerts,” and wrong-number scams. Text scam losses hit $470 million in 2024 — five times higher than 2020 despite fewer reports. Phishing pages average 21 hours online.
What to capture:
- • The phishing text/email with sender information
- • The fake login page (URL is key — it reveals the real domain)
- • Email headers (to identify the actual sending server)
- • Any credentials you entered (to know what to change immediately)
- • Subsequent unauthorized transactions on your real accounts
Job & Employment Scams (“Task Scams”)
$501M losses (FTC, 2024) — reports tripled since 2020These typically involve fake remote job offers that require “equipment fees,” “training deposits,” or “background check payments.” Task scams ask you to complete small paid tasks, then demand a deposit to “unlock” earnings. Reports have tripled since 2020.
What to capture:
- • The job listing or recruitment message
- • The company’s website (often a clone of a real company)
- • The “offer letter” or contract
- • All communication with the “recruiter” (email, WhatsApp, Telegram)
- • Payment requests for equipment, training, or deposits
- • The task platform interface (if task scam)
A customer orders a “handmade Italian leather” jacket for $289 from an Instagram ad. What arrives is a $15 synthetic knockoff. When they go back to the website, the description has been changed to “leather-style.”
With ProofSnap: The customer captured the product page before purchasing. The evidence ZIP contains the original description, the price, full page HTML, and a blockchain timestamp. The bank receives a timestamped PDF proving what the website showed on the purchase date. Chargeback filed under Visa 13.3 — compelling evidence standard met.
This is why Step 2 and the Capture-Before-You-Pay rule matter. See more examples below.
3. How Do You Capture Evidence of an Online Scam?
THE FIRST 60 MINUTES ARE CRITICAL
Scam websites go offline, profiles get deleted, and chat histories vanish. Follow this sequence immediately when you suspect or confirm a scam. Do not wait until tomorrow. Every hour you delay reduces your chance of recovery.
Stop — Do NOT Close Anything
Do not close browser tabs. Do not delete messages. Do not confront the scammer. Do not report the profile yet. Every open tab and message thread is evidence. Closing or reporting triggers deletion.
Capture the Scam Page with Full Metadata
Use a forensic web capture tool to record the scam website or listing. A proper capture includes:
- • Full-page screenshot (not just the visible viewport)
- • Page URL with exact timestamp
- • HTTP headers and TLS certificate (identifies the real server)
- • Complete page HTML and DOM text content
- • Cookies and localStorage (proves you were logged in)
- • SHA-256 cryptographic hash (tamper detection)
Document All Communications
Capture every conversation: WhatsApp Web, Telegram, Facebook Messenger, email threads, Discord channels, dating app chats. Scroll through the entire conversation history before capturing. Include the scammer’s profile page separately.
Record Payment Details
Capture your bank or card statement showing the transaction, payment confirmation pages, crypto transaction hashes (from your exchange and from the blockchain explorer), PayPal/Venmo/Zelle receipts, and any invoices or payment links the scammer provided.
Anchor Evidence to the Blockchain
Generate a SHA-256 hash of every evidence file and anchor it to a blockchain timestamp. This creates an independent, tamper-proof record that the evidence existed at a specific point in time. Under FRE 902(13)–(14) and eIDAS 2, cryptographically signed timestamps have legal standing.
Supplementary evidence: Check if the scam website was archived by the Wayback Machine (web.archive.org). If the site operated for weeks, it may have been crawled — providing an independent, third-party record that corroborates your own captures. You can also manually save a page using web.archive.org/save.
Contact Your Bank Immediately
Call your bank’s fraud department. Request a chargeback (credit/debit card) or transaction freeze (bank transfer). The FBI’s Recovery Asset Team froze $561 million in fraudulent funds in 2024 with a 66% success rate — but speed is critical. For bank transfers, acting within 24–72 hours dramatically increases recovery chances.
File Reports with Authorities
Report to all applicable agencies (see Section 4 below). Attach your forensic evidence package. The more detailed your evidence, the higher the chance of investigation and recovery. Request a case/reference number for your bank dispute.
One click. One ZIP. Everything your bank and police need.
ProofSnap turns any web page into a court-ready evidence package. Here is what you get for every capture:
proofsnap_20260220_141532.zip
screenshot.jpeg ← full-page scroll capture
metadata.json ← URL, timestamp, HTTP headers, TLS cert, cookies
page.html ← complete page source code
domtextcontent.txt ← all visible text on the page
evidence.pdf ← court-ready PDF with all evidence + hashes
forensic_log.json ← capture process log
chain_of_custody.json ← who captured what, when, how
manifest.json ← SHA-256 hash of every file
manifest.sig ← RSA-4096 digital signature
manifest.json.ots ← Bitcoin blockchain timestamp (OpenTimestamps)
publickey.pem ← public key for signature verification
How it works in practice — click extension, capture, download ZIP, verify:
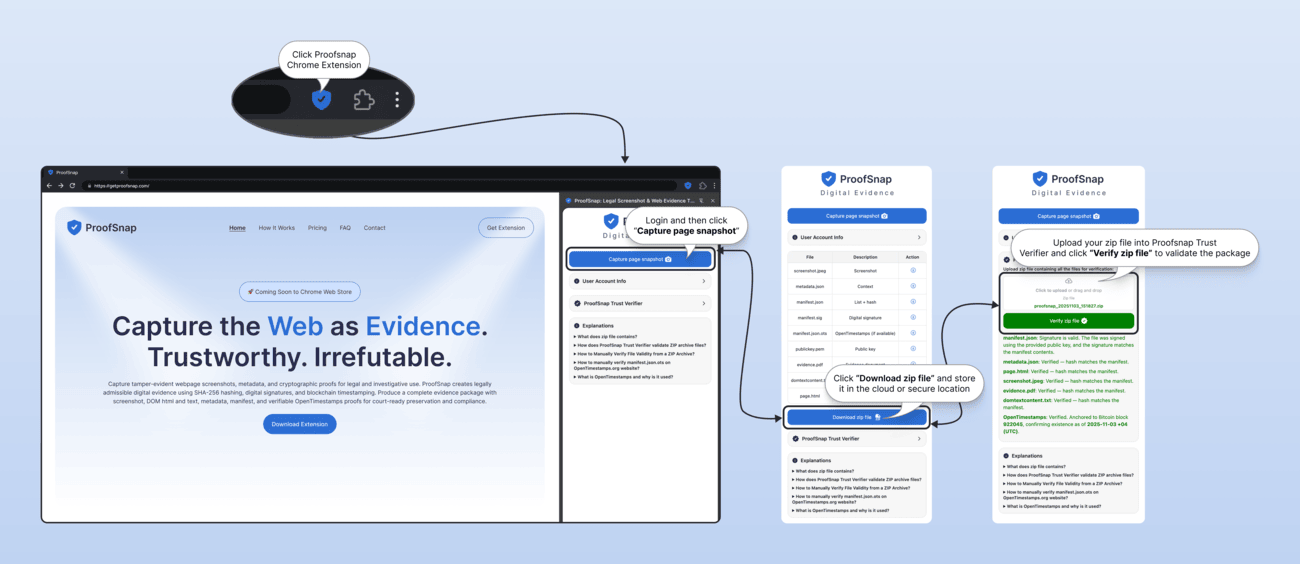
This is what “forensic evidence” looks like. Your bank gets a timestamped PDF. The police get full metadata. A court gets a blockchain-anchored chain of custody. Takes about 30 seconds per capture.
4. Where Do You Report an Online Scam? (IC3, Action Fraud & Global Agencies)
In the US, report to IC3 (ic3.gov) and the FTC. In the UK, report to Report Fraud (formerly Action Fraud). In the EU, report to your national cybercrime unit and Europol. Report to every applicable agency — multiple reports increase the chance your case is investigated.
| Country | Primary Agency | Website | Also Report To |
|---|---|---|---|
| United States | FBI IC3 (Internet Crime Complaint Center) | ic3.gov | FTC ReportFraud, state AG, local police |
| United Kingdom | Report Fraud (replaced Action Fraud Dec 2025) | reporting.actionfraud.police.uk | Your bank’s fraud team, local police (101) |
| EU (general) | National cybercrime unit (varies by country) | europol.europa.eu | Your bank, consumer protection authority |
| Germany | Onlinewache (state police portal) | Varies by Bundesland | Verbraucherzentrale, BaFin (financial fraud) |
| France | THESEE (plainte en ligne) | service-public.fr | Signal-Spam, Pharos, DGCCRF |
| Australia | Scamwatch (ACCC) | scamwatch.gov.au | ReportCyber (ACSC), your bank |
| Canada | Canadian Anti-Fraud Centre (CAFC) | antifraudcentre.ca | Local police, your bank |
| India | National Cyber Crime Reporting Portal | cybercrime.gov.in | Helpline 1930, local police (FIR), RBI (banking fraud) |
| Japan | Prefectural Police Cybercrime Division | npa.go.jp/cyber | National Consumer Affairs Center (NCAC), your bank |
Tip for all countries: When filing a police report, ask to speak with an officer or detective who specializes in financial crimes or cybercrime. Provide your case reference number to your bank when disputing transactions.
Also Report Directly to the Platform
In addition to government agencies, report the scammer on the platform where the scam occurred. Platform reports help prevent other victims and create an internal record that law enforcement can subpoena.
Important: Capture the scammer’s profile and all conversations before reporting. Once reported, the account and its content may be deleted within hours.
5. How to Get a Chargeback After Fraud (Visa 13.3, Mastercard 4853)
Yes, you can get your money back if you paid by credit or debit card. A chargeback is often the fastest way to recover funds — you have 120 days to file. Use Visa reason code 13.3 or Mastercard 4853 for items not as described, or Visa 10.4 / Mastercard 4837 for unauthorized fraud. The key is having the right evidence for the right reason code:
| Scenario | Visa Code | Mastercard Code | Deadline | Evidence Needed |
|---|---|---|---|---|
| Item not as described / counterfeit | 13.3 | 4853 | 120 days | Original listing + what you received |
| Merchandise never received | 13.1 | 4855 | 120 days from expected delivery | Order confirmation + delivery window |
| Unauthorized / fraudulent transaction | 10.4 | 4837 | 120 days | Proof you did not authorize the charge |
| Recurring charge after cancellation | 13.2 | 4841 | 120 days | Cancellation confirmation + subsequent charge |
Why Forensic Evidence Wins Chargebacks
Under Visa and Mastercard’s compelling evidence rules, the card network decides based on whose documentation is stronger. A timestamped forensic capture of the original product listing — with SHA-256 hash, page HTML, server certificates, and blockchain timestamp — is objectively stronger than a screenshot. It proves what the merchant’s website displayed at the time of your purchase and that the evidence has not been altered.
Crypto and bank transfers: Chargebacks do not apply to cryptocurrency, wire transfers, gift cards, or peer-to-peer payment apps (Zelle, Venmo “Friends & Family”). For these, contact your bank’s fraud department immediately and file with IC3/law enforcement. The FBI’s Financial Fraud Kill Chain can sometimes freeze wire transfers if reported within 72 hours.
6. Legal Standards: FRE 901, eIDAS 2 & Court Admissibility
Yes, forensic web captures are admissible as evidence. In the US, FRE 902(13)–(14) allows self-authenticating machine-generated records with cryptographic verification. In the EU, eIDAS 2 gives qualified electronic timestamps a legal presumption of accuracy across all member states. Here is what each jurisdiction requires:
United States: FRE 901 & 902
Under Federal Rule of Evidence 901, the party presenting digital evidence must prove it is what they claim it to be. The opposing party can challenge its authenticity. A plain screenshot is vulnerable to this challenge.
FRE 902(13) and 902(14), amended in 2017, allow machine-generated records and digitally copied data to be self-authenticating when accompanied by a qualified certification. Forensic captures with cryptographic hashes and chain-of-custody documentation qualify under these provisions.
New in 2025: Proposed Rule 707, released for public comment in August 2025, will specifically address authentication standards for AI-generated and machine-generated evidence — recognizing that deepfakes make traditional authentication insufficient.
European Union: eIDAS 2
Under EU Regulation 2024/1183 (eIDAS 2), qualified electronic timestamps have a legal presumption of accuracy across all EU member states (iuris tantum). The burden of proof shifts to whoever challenges the timestamp, with a required accuracy of 1 second (metrological sources reach 50 nanoseconds).
A Marseille court accepted blockchain evidence in March 2025. Bitcoin-anchored timestamps using the RFC 3161 standard combined with OpenTimestamps provide an independent, tamper-proof record recognized across jurisdictions.
United Kingdom
UK courts assess digital evidence under the Civil Evidence Act 1995 and the Police and Criminal Evidence Act 1984 (PACE). While there is no specific equivalent to FRE 902 for self-authenticating digital evidence, courts increasingly expect proper chain of custody and integrity verification for electronic evidence. Blockchain timestamps are accepted as corroborating evidence when supported by expert testimony or technical documentation.
7. Prevention: What to Do Before You Pay
The best evidence is evidence you never need. Here are the warning signs that a transaction may be fraudulent:
Red Flags: Websites
- • Domain registered in the last 30 days (check WHOIS)
- • No physical address or phone number
- • Prices 50%+ below market value
- • Only accepts wire transfer, crypto, or gift cards
- • Poor grammar but professional-looking design
- • No social media presence or reviews
Red Flags: People
- • Moves conversation off-platform immediately
- • Refuses video calls or always has “connection issues”
- • Creates urgency (“deal expires today,” “account locked”)
- • Asks for payment via unusual methods
- • Profile photos reverse-search to different identities
- • “Guaranteed returns” on investments
The Capture-Before-You-Pay Rule
If you are making a significant online purchase from an unfamiliar seller, capture the listing page before completing the transaction. This takes 30 seconds and gives you timestamped proof of what was advertised if the seller later changes the listing, disappears, or sends something different. Think of it as a receipt for what was promised.
8. After a Scam: Protect Yourself from Further Damage
Being scammed once makes you a target for secondary attacks. Take these steps immediately after securing your evidence and contacting your bank.
Beware of “Recovery Scams”
Scammers sell lists of victims to other criminals. After being scammed, you may be contacted by people claiming they can “recover your money” for an upfront fee. These “recovery agents” are scammers themselves.
- • No legitimate law enforcement agency or bank will contact you asking for a fee to recover funds
- • “Crypto recovery experts” on social media are almost always fraudulent
- • Lawyers and legitimate recovery firms never guarantee results or ask for large upfront payments via crypto or wire transfer
- • The FTC and IC3 specifically warn about recovery scams targeting previous victims
Protect Your Identity
If you shared personal information with a scammer (name, address, date of birth, Social Security number, bank details, ID copies), take these steps to prevent identity theft:
United States
- • Place a credit freeze at all three bureaus: Experian, Equifax, TransUnion
- • Set up a fraud alert (free, one call to any bureau alerts all three)
- • Report identity theft at identitytheft.gov
- • Monitor your credit reports at annualcreditreport.com
United Kingdom & EU
- • UK: Register with CIFAS Protective Registration (£25 for 2 years)
- • Check your credit with Experian, Equifax, or TransUnion UK
- • EU: Contact your national data protection authority if personal data was compromised
- • Notify your bank and request enhanced verification on your accounts
Always do: Change passwords for any accounts you shared with the scammer. Enable two-factor authentication (2FA) on your email, banking, and social media accounts. Use a password manager to create unique passwords for every account.
It Is Not Your Fault
Only an estimated 5% of fraud victims report the crime. Many stay silent due to shame or embarrassment. Modern scams are sophisticated, well-funded, and specifically designed to exploit trust. Being scammed is not a reflection of intelligence — it is a crime committed against you.
If you are struggling emotionally, the following resources offer free, confidential support: US: AARP Fraud Helpline (877-908-3360) • UK: Victim Support (0808 168 9111) • Community: r/Scams (Reddit community with 1M+ members)
9. Screenshot vs. Forensic Evidence: What Gets Accepted?
| Capability | Regular Screenshot | Forensic Capture |
|---|---|---|
| Visual content of the page | Yes | Yes (full-page scroll) |
| Independent timestamp proof | No | Yes (blockchain) |
| Tamper detection (SHA-256) | No | Yes |
| Page HTML and DOM content | No | Yes |
| HTTP headers & TLS certificate | No | Yes |
| Cookies & session data | No | Yes |
| Chain of custody log | No | Yes (automated) |
| Digital signature (RSA-4096) | No | Yes |
| Evidence PDF for court | No | Yes |
| FRE 902 self-authenticating | No | Yes (902(13)/(14)) |
| eIDAS 2 qualified timestamp | No | Yes (blockchain) |
One successful chargeback pays for 18 years of ProofSnap.
The average online fraud loss is over $19,000 (FBI IC3, 2024). ProofSnap costs $8.99/month. If forensic evidence helps you win even one dispute, the tool has paid for itself hundreds of times over.
10. Frequently Asked Questions
Can I use screenshots as evidence of an online scam?
Regular screenshots are increasingly rejected because they have no metadata, no timestamp proof, and no chain of custody. Under FRE 901 and eIDAS 2, digital evidence must be authenticated. Forensic captures with SHA-256 hashes and blockchain timestamps meet this standard. See Section 1 and the comparison table for details.
What evidence do police need to investigate an online scam?
Scammer contact details, transaction records, communication records, timestamped website captures, and any shared identity documents. Forensic captures with metadata are significantly more useful than screenshots. See the step-by-step guide and reporting table.
How do I report an online scam to IC3?
File at ic3.gov with victim info, transaction details, subject info, and a narrative. IC3 received 859,532 complaints in 2024 ($16.6B in losses). The FBI Recovery Asset Team froze $561M with a 66% success rate. See Section 4 for all countries.
How long do scam websites stay online?
Phishing pages: ~21 hours. Fake shops: 2–8 weeks. Romance scam profiles: deleted within hours of being reported. This is why immediate capture is critical. See the step-by-step guide.
Can I get a chargeback for an online scam?
Yes, if you paid by card. Key codes: Visa 13.3 / Mastercard 4853 (not as described), Visa 10.4 / Mastercard 4837 (fraud). Deadline: 120 days. Does not apply to crypto, wire transfers, or gift cards. See Section 5 for the full chargeback code table.
What is the best way to document a romance scam?
Capture the profile (photos, bio), all conversations, reverse-image search results, payment receipts, and any sites they linked to. Do this before confronting or reporting — they delete everything immediately. $672M in losses in 2024. See scam type #4 for the full checklist.
How do I document a crypto or investment scam?
Capture the platform interface, wallet addresses (Etherscan/Blockchain.com), all communication, the recruitment message, and blocked withdrawal attempts. $9.3B in losses in 2024. See scam type #1 for the full checklist.
What evidence do banks need for a fraud dispute?
Original transaction proof, evidence that goods were not as described or never delivered, proof of merchant contact attempt, and scam documentation. Forensic captures with timestamps are stronger than screenshots under compelling evidence rules. See Section 5.
Is a blockchain timestamp admissible in court?
Yes. US: FRE 902(13)/(14) allows self-authenticating machine-generated records. EU: eIDAS 2 qualified timestamps have legal presumption of accuracy. A Marseille court accepted blockchain evidence in March 2025. See Section 6 for full legal analysis.
What should I do immediately if I think I have been scammed?
Act within 60 minutes: (1) Do NOT close tabs or delete messages. (2) Capture everything with forensic tools. (3) Call your bank. (4) File with IC3/Report Fraud. (5) Change compromised passwords. See the step-by-step guide and the quick reference checklist.
How much money do people lose to online scams?
In 2024: $16.6B (FBI IC3), $12.5B reported / ~$196B estimated (FTC), £1.17B (UK), €4.2B (EU). Largest categories: crypto $9.3B, investment $5.7B, imposter $2.95B. See the full statistics breakdown.
Can AI-generated deepfakes be used in scams? How do I prove it?
Yes — AI photos, videos, and voice for romance, impersonation, and investment scams. Capture fake content with forensic tools, run reverse-image searches, document inconsistencies. Proposed FRE Rule 707 (August 2025) will address AI-generated evidence authentication. See Section 6.
Will my bank refund money lost to an online scam?
It depends on how you paid. Credit cards offer the strongest protection — federal law limits liability to $50, and most banks refund 100% of verified fraud. Debit cards are protected if reported within 2 business days ($50 max) or 60 days ($500 max). Wire transfers, crypto, gift cards, and Zelle/Venmo are extremely difficult to recover. For card payments, file a chargeback under Visa 13.3 or Mastercard 4853 within 120 days. Forensic evidence with timestamps significantly improves your chances. See Section 5 for the full chargeback code table.
Can police actually investigate an online scam?
Yes, but it depends on the amount, evidence quality, and whether the scam is part of a larger pattern. The FBI’s IC3 received 859,532 complaints in 2024, and their Recovery Asset Team froze $561M with a 66% success rate — but only for cases reported quickly with strong evidence. Local police often lack cybercrime resources, so filing with IC3 (US) or Report Fraud (UK) is critical — they aggregate complaints to identify patterns. Forensic evidence with metadata and chain of custody significantly increases the chance your case is prioritized. See Section 4.
How Forensic Captures Work in Practice
A buyer pays $1,800 for a MacBook Pro on Facebook Marketplace via a payment link the seller sends in Messenger. The seller’s profile shows 3 years of history and positive reviews. After payment, the seller stops responding. The listing is deleted. The profile turns out to be hacked.
With ProofSnap: Before paying, the buyer captures the Marketplace listing (photos, price, seller profile link), the Messenger conversation, and the payment page. After the scam, the forensic evidence package proves the listing existed, what was promised, and that the payment went to that specific seller — even though the listing and profile are now deleted. Police get metadata linking the payment page to the seller. Chargeback filed under Mastercard 4853.
A victim meets someone on a dating app who claims to be a US military officer stationed overseas. Over 3 months, they build a relationship via WhatsApp. The scammer asks for $12,000 for “emergency medical bills.” After the wire transfer, the dating profile is deleted and the WhatsApp number goes silent.
With ProofSnap: Before the profile disappears, the victim captures the dating profile (photos, bio, joined date), the WhatsApp conversation (full scroll), and the wire transfer confirmation page. Each capture is SHA-256 hashed and blockchain-timestamped. The IC3 report includes forensic evidence showing the scammer’s profile existed, the conversation timeline, and the payment — all with tamper-proof chain of custody. The FBI’s Recovery Asset Team uses the bank details to attempt a wire recall within 72 hours.
A Telegram contact introduces a victim to a “trading platform” showing 40% monthly returns. The victim deposits $5,000 in Bitcoin. The dashboard shows profits growing. When they try to withdraw, the platform demands a “tax deposit” of $2,000. The platform URL changes weekly.
With ProofSnap: The victim captures the fake trading dashboard (showing the fabricated balance), the “tax deposit required” message, the Telegram conversation, and the Bitcoin transaction on a blockchain explorer. The blockchain timestamp proves the fake platform existed and displayed specific content on specific dates — even after the URL changes. Police and IC3 receive a forensic evidence package linking the scammer’s wallet addresses to the fake platform.
Key Takeaways
- • $16.6 billion in internet crime losses reported to the FBI in 2024 (up 33%)
- • Scam content disappears fast — phishing pages average 21 hours online, fake shops 2–8 weeks
- • Screenshots are the weakest evidence — no timestamp proof, easily fabricated, no metadata
- • Forensic captures with SHA-256 hashes and blockchain timestamps meet FRE 901/902 (US) and eIDAS 2 (EU) standards
- • Chargeback codes: Visa 13.3, Mastercard 4853 (not as described); Visa 10.4, Mastercard 4837 (fraud)
- • Report to all agencies: IC3 (US), Report Fraud (UK), national cybercrime unit (EU) + your bank
- • Act within 60 minutes — do not close tabs, capture everything, then contact your bank
- • FBI Recovery Asset Team froze $561M in fraudulent funds in 2024 with 66% success rate
Quick Reference Checklist
Bookmark or print this page. Follow these steps immediately if you suspect a scam.
Immediate (first 60 minutes)
- ☐ Do NOT close browser tabs or delete messages
- ☐ Capture scam website / listing (full-page forensic capture)
- ☐ Capture scammer’s profile page
- ☐ Capture all chat / email conversations
- ☐ Capture payment confirmations & bank statements
- ☐ Generate SHA-256 hashes + blockchain timestamps
- ☐ Call your bank’s fraud department
Within 24 hours
- ☐ File with IC3 (US) / Report Fraud (UK) / cybercrime unit (EU)
- ☐ File with FTC at reportfraud.ftc.gov (US)
- ☐ Report scammer on the platform (FB, Tinder, eBay...)
- ☐ Initiate chargeback with card issuer (if applicable)
- ☐ Change passwords + enable 2FA on compromised accounts
- ☐ Place credit freeze (if you shared personal info)
- ☐ Save all evidence to two locations (local + cloud)
11. Sources & References
- • FBI IC3 — 2024 Internet Crime Report (859,532 complaints, $16.6B losses)
- • FTC — Consumer Fraud Losses 2024 ($12.5B reported, $196B estimated)
- • UK Finance — Fraud Report 2024 (£1.17B stolen)
- • National Crime Agency — NSA 2025 Fraud Assessment (3.9M incidents, 41% of crime)
- • EBA/ECB — Joint Report on Payment Fraud 2025 (€4.2B in EU/EEA)
- • Pew Research — 73% of US Adults Hit by Online Scams (2025)
- • TRM Labs — FBI IC3 2024 Analysis ($9.3B crypto losses, 66% increase)
- • FBI — Operation Level Up (4,300+ crypto scam victims identified)
- • Cornell LII — Federal Rules of Evidence 901 (Authentication)
- • Cornell LII — Federal Rules of Evidence 902 (Self-Authenticating Evidence)
- • Esquire Deposition Solutions — Proposed FRE Rule 707 for Deepfake Evidence
- • European Commission — eIDAS 2 Regulation (Qualified Electronic Timestamps)
- • Chargebacks911 — Visa Reason Code 13.3 (Not as Described)
- • Chargebacks911 — Mastercard Reason Code 4853 (Defective/Not as Described)
Related Articles
How to Win a Chargeback: Item Not as Described
Visa 13.3, Mastercard 4853 step-by-step evidence guide Digital EvidenceWhy Regular Screenshots Fail in Court in 2026
eIDAS 2, FRE 901, and the new rules for digital evidence Legal GuideAre Screenshots Admissible in Court?
Complete FRE 901 and FRE 902 authentication guide for lawyers AI & EvidenceWho’s Liable When Your AI Lies?
EU AI Act, deepfakes, and the AI Flight Recorder conceptImportant Notice: This article is for informational purposes only and does not constitute legal advice. While the content has been carefully researched using official government sources (FBI IC3, FTC, UK Finance, EBA/ECB, Cornell LII), it makes no claim of completeness or timeliness. For legal questions specific to your situation, consult a licensed attorney in your jurisdiction. ProofSnap assumes no liability for decisions made based on this article. Fraud statistics, chargeback reason codes, and legal standards may change — always verify current guidelines with your bank and local authorities.